Singapore Fintech Innovation Seminar – Security and Compliance Automation
The rapid growth of digital payments worldwide and the increasing presence of FinTech startups have given rise to sophisticated fraud schemes, financial losses, and personal data breaches. In response, regulators, payment networks, and industry organizations have introduced a continuous stream of complex and evolving compliance requirements to safeguard the payment industry. Complying with these regulations is a formidable challenge, even for large organizations, and can spell disaster for smaller players if neglected.
Media Report:Breaching the New Frontier in Payments Security and Compliance Automation – Fintech Singapore (fintechnews.sg)

Resource sharing
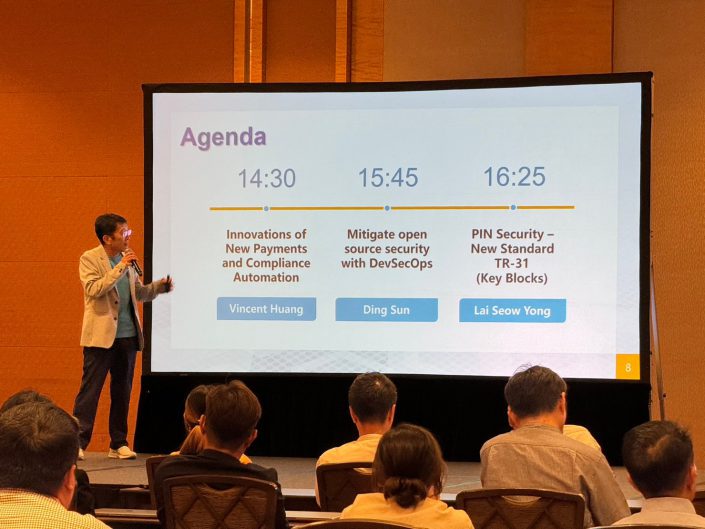
Topic:Innovation of New Payments and Compliace Automation
Speaker:Vincent Huang – PCI DSS QSA, Secure Vectors Information Technology Inc.
Topic:Mitigate open source security with DevSecOps
Speaker:Ding Sun – Head Engineering, Scantist Pte. Ltd.
Topic:PIN Security – New Standard TR-31 (Key Blocks)
Speaker:Lai Seow Yong – APAC Technical Pre-sales Manager, Utimaco Management GmbH
Topic:Leading in the AI Era
Speaker:Cheah Sook Hoon
Notes and Legal Disclaimer
- Final Usage Rights Reserved: The author retains exclusive rights to the use of this presentation (referred to as the “document”). Unauthorized modification, reproduction, distribution, or any other use is strictly prohibited without the author’s written consent.
- Non-Commercial Use Only: Users are allowed to use the document solely for personal or non-commercial purposes. Any commercial use, including sale or distribution for profit, requires prior written approval from the author.
- Disclaimer of Liability: The document’s content is for reference only, and the author is not liable for any direct or indirect losses incurred from its use. Users assume all associated risks.
- Intellectual Property Protection: All content in the document, such as text, images, and charts, is protected by intellectual property laws. Unauthorized use is prohibited without the author’s explicit permission.